Russian Rosoboronexport Massive Leak
Russian Rosoboronexport Massive Leak - Hackers consider themselves to Anonymous, posted on the Web internal documents of the Russian Defence Export...
Find the latest network security news, articles, product reviews, comparisons and analysis
 Okta Customer Support System Hacked, Sensitive Data Stolen
Okta Customer Support System Hacked, Sensitive Data Stolen
 LastPass Data Breach Exposes Encrypted Password Vaults
LastPass Data Breach Exposes Encrypted Password Vaults
 Using Ethical Hacking to Quickly Decode Hashes and Uncover Vulnerabilities
Using Ethical Hacking to Quickly Decode Hashes and Uncover Vulnerabilities
 A Casino Database Gets Hacked Through a Smart Fish Tank Thermometer
A Casino Database Gets Hacked Through a Smart Fish Tank Thermometer
 Ransomware Attack Exposes 1.5TB of Stolen Aerospace Data
Ransomware Attack Exposes 1.5TB of Stolen Aerospace Data
Russian Rosoboronexport Massive Leak - Hackers consider themselves to Anonymous, posted on the Web internal documents of the Russian Defence Export...
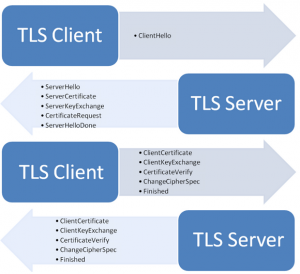
New flaw found in TLS cryptographic protocol. The flaw was uncovered by security researchers at the French National Institute for...
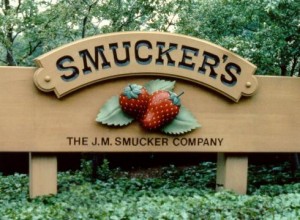
The web site of Smuckers Hacked and customer names, addresses, e-mail addresses, phone numbers, credit card numbers, expiration dates and verification codes...
Moscow based Russia's biggest news channel website Russia Today hacked. RT.com website was defaced by an unknown group of hackers...
The service known for hosting millions of Web sites Namecheap is under a massive DDoS attack. On Thursday morning, 300...